-
Network topology: Best practices for modern networks
A well-designed network starts with a clear understanding of its structure. Network topology is the blueprint of how devices and connections interact, and it plays a key role in determining a network�...
-
Managed DNS: Your complete guide to understanding and implementation
The Domain Name System (DNS) is a foundational component of every organization’s IT infrastructure. A reliable DNS service not only ensures fast query resolution and minimizes downtime, but it also ...
-
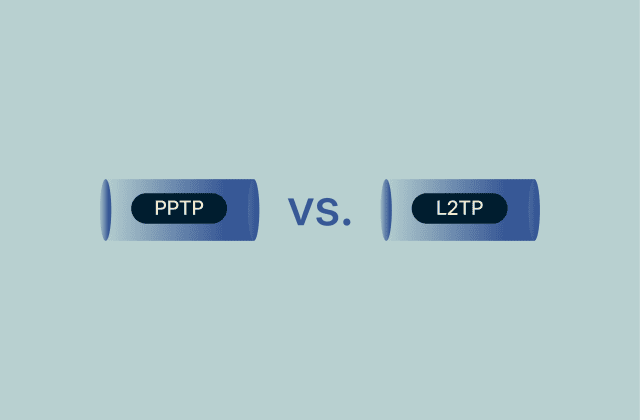
PPTP vs. L2TP: What’s the difference?
The Point-to-Point Tunneling Protocol (PPTP) and Layer 2 Tunneling Protocol (L2TP) are both virtual private network (VPN) tunneling protocols, but they function very differently. All VPNs direct inter...
-

How to delete your Threads account without deleting Instagram
When Threads was first launched, you weren’t able to delete it without also deleting the Instagram account you used during account creation. Fortunately, Meta has now added the ability to deactivate...
-
What is a shared IP address? Understanding shared and dedicated IPs
Your Internet Protocol (IP) address may seem like just a technical detail, but it plays a key role in how you appear online. For digital marketers, small business owners, or anyone managing a website ...
-

What is cybersecurity? A simple guide for beginners
Cybersecurity affects nearly every aspect of daily life. From the phone in your pocket and laptop on your desk to smart devices in your home, all rely on strong protections to keep you safe. Without p...
-

Identity theft insurance: What it is and whether it’s worth it
Online identity theft is a widespread problem that can happen when you least expect it. If criminals gain access to your personal data, dealing with the fallout can be stressful, time-consuming, and e...
-
Internet fraud: Definition, types, prevention, and recovery
Internet fraud keeps growing every year, and the numbers are staggering. Scammers are stealing billions of dollars from people and businesses worldwide, and there’s no sign of it slowing down. The d...
-
What is Blowfish encryption, and how does it work?
Blowfish is a fast, flexible encryption algorithm designed to protect data using a shared secret key. While it’s an older algorithm, it’s still commonly used in legacy systems and for password has...
-
Who can see my mobile data history?
More people can see your mobile data history than you might expect. Your mobile carrier, internet service provider (ISP), the websites you visit, and network admins can all see varying amounts of your...

Don't miss the Spring Deal: Save up to 78% before April 21.
Don't miss the Spring Deal: Save up to 78% before April 21. Claim now!
Claim Now!

