-
Spam vs. phishing: Key differences and how to stay safe online
Most people’s inboxes are full of “spam” messages: sales emails, newsletters you never signed up for, or random promotions. While these messages can be annoying, they’re not inherently dangero...
-

How to identify and remove the Windows Defender Security Center scam
Fake Windows Defender Security Center alerts are a common online scam. They’re designed to do one thing: make you panic. These messages often look official, sound urgent, and warn you about serious ...
-
How to set up a static IP address (step-by-step guide)
If you need to consistently reach a device, such as a gaming server or a smart-home hub, you don't want its Internet Protocol (IP) address to change in the background. Assigning a static IP gives it a...
-

What is encrypted DNS, and why does it matter?
Every time you visit a website, your device asks a Domain Name System (DNS) server to find the website's IP address. But here’s the catch: traditional DNS requests travel in plaintext, so anyone int...
-
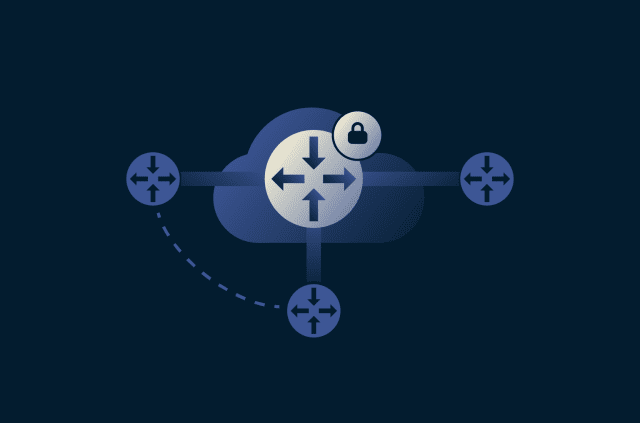
What is dynamic multipoint VPN (DMVPN)?
As networks expand across multiple offices and cloud environments, keeping every site securely connected becomes a challenge. Traditional virtual private network (VPN) setups often struggle to scale w...
-

What is shimming in cybersecurity, and how can you protect against it?
When you use a device or an app, it doesn’t handle every task by itself. To work properly, it relies on other parts of the same system to do specific jobs. A payment terminal relies on software to p...
-
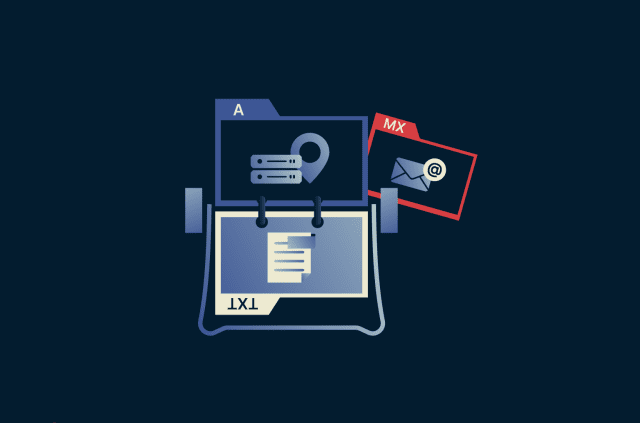
DNS record types explained: A complete guide for privacy
The Domain Name System (DNS) is a core piece of internet infrastructure, responsible for translating domain names into IP addresses so internet traffic can be routed correctly and facilitating communi...
-
What is MAC address spoofing?
MAC address spoofing is the practice of changing a device’s Media Access Control (MAC) address so it appears to be a different device on a network. Every device that connects to a network, including...
-

How to stop getting spam texts and stay safe
Spam texts add unwanted messages to your inbox, increasing message volume and making it harder to keep track of legitimate conversations and alerts. But they aren’t just an annoyance. While some spa...
-
Types of VPNs: Complete guide to VPN categories and protocols
All virtual private networks (VPNs) work on the same principle: they encrypt your internet traffic and route it through a secure server. Where they differ is in how they’re designed to be used. Some...
Featured







